Automated Threat Modeling for Connected Vehicles
SPRING 2020 RESEARCH INCUBATION AWARDEE
PI: David Starobinski, Professor, Electrical & Computer Engineering and Systems Engineering, ENG
Special Track: Honda Research Institute Europe
What is the Challenge?
Misbehavior by compromised vehicles represents a significant threat to connected vehicle technology. Specifically, a compromised vehicle that has authenticated credentials allowing it to communicate with other vehicles freely. With this privilege, an attacker could use the compromised vehicle to send bogus BSMs containing information that can compromise the safety of the people within the premises of the vehicle.

What is the Solution?
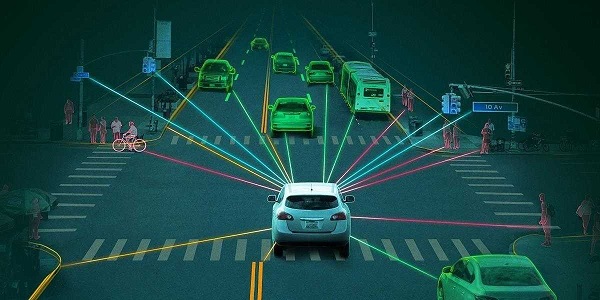
Connected vehicles could dramatically reduce the number of fatalities and serious injuries caused by accidents on our roads and highways. These vehicles periodically broadcast basic safety messages (BSMs) that provide absolute values for position, time, heading, and velocity within a communication range to ensure awareness for other connected vehicles. BSMs enhance traffic safety and efficiency by allowing vehicles and roadside units (RSUs) to convey information on surrounding events; some of these events include notifying and warning other vehicles about braking actions of the vehicle in front, including warning other vehicles about upcoming traffic jams.
What is the Process?
David Starobinski, Faculty Affiliate of the CRI Lab at the Hariri Institute for Computing focuses on freely available tools, with an emphasis on studying their modularity and scalability:
The tools are as follows: (i) OWASP Threat Dragon (TD): TD is not only an online threat modeling web application but also a desktop application, which includes system diagramming and a rule engine to auto-generate threats/mitigation.
He then selects one of those tools (popularly TD because as it is open-source) and performs a threat assessment for one modality (i.e., a Level 1 autonomous car). The goal would be to demonstrate and enhance the capability of the tool to capture a wide range of threats for misbehavior detection in vehicular environments. The next step would be to expand the tool capability to automate the task of threat modeling to other modalities (i.e., vehicles with higher levels of autonomy).