Phishing
Phishing is a scam intended to steal personal and financial information from unsuspecting victims. Passwords, credit card numbers, bank account information, Social Security number, or other sensitive information–all are valuable to scam artists.
SMiShing
A form of phishing, SMiShing is when someone tries to trick you into giving them your private information or click on a link via a text (SMS message.) Put simply, SMiShing is any kind of phishing that involves a text message. SMiShing is particularly effective because people tend to be more inclined to trust a text message than an email. Most people are aware of the security risks involved with clicking on links in emails but less true when it comes to text messages.
For more information on SMiShing check out: https://www.fcc.gov/avoid-temptation-smishing-scams
Spear Phishing
Spear phishing involves highly specialized attacks against specific targets or small groups of targets to collect information or gain access to systems. For example, a cybercriminal may launch a spear phishing attack against a business to gain credentials to access a list of customers. From that attack, they may launch a phishing attack against the customers of the business. Since they have gained access to the network, the email they send may look even more authentic and because the recipient is already customer of the business, the email may more easily make it through filters and the recipient maybe more likely to open the email.
The cybercriminal can use even more devious social engineering efforts such as indicating there is an important technical update or new lower pricing to lure people.
How to avoid being phished
Most people think they are pretty knowledgeable about spam and phishing, yet every day someone at Boston University falls for a common email scam and has their account compromised.Be proactive in protecting yourself. Phishing emails come in many forms and though the most important thing you can do is to avoid them altogether, here are some useful tips to avoid getting hooked:
Tips for Being Safe Online
When in doubt, throw it out: Links in email, tweets, posts and online advertising are often how cybercriminals try to compromise your information. If it looks suspicious, even if you know the source, it’s best to delete or – if appropriate – mark it as junk.
Think before you act: Be wary of communications that implores you to act immediately, offers something that sounds too good to be true or asks for personal information.
Make your passphrase a sentence: A strong passphrase is a sentence that is at least 12 characters long. Focus on positive sentences or phrases that you like to think about and are easy to remember (for example, “I love country music.”). On many sites, you can even use spaces!
Unique account, unique passphrase: Having separate passphrases for every account helps to thwart cybercriminals. At a minimum, separate your work and personal accounts and make sure that your critical accounts have the strongest passphrases.
Lock down your login: Fortify your online accounts by enabling the strongest authentication tools available, such as biometrics, security keys or a unique one-time code through an app on your mobile device. Your usernames and passphrases are not enough to protect key accounts like email, banking and social media.
Don't click the provided link
It is trivially easy to make a link lie to you. Instead of clicking a provided link, use your browser to go to the known and trusted website by typing the link into your web browser yourself.For example, take this link: http;//www.google.com/ If you click this, it will not take you to Google, it will take you somewhere completely different. Scammers use this trick all the time to trick you to going to malicious websites.You can tell where a link is going to take you by hovering over it with your mouse. Don’t click. Hover. If you do this for the link above you will see “onguardonline.gov” pop up in a box by your pointer or in a space at the bottom of your email client or browser.
If you are on a smartphone, click and hold the link to have a box appear that will show you the real destination and ask if you really want to go there.
General rule: if the email message is lying to you about where it wants to send you, it is a scam.
Monitor your security
- If you are concerned about your account, contact the organization using a phone number you know to be genuine, or open a new Internet browser session and type in the company’s correct Web address yourself.
- Use anti-virus and anti-spyware software, as well as a firewall, and update them all regularly.
- Never share your personal or financial information.
- Review credit card and bank account statements as soon as you receive them to check for unauthorized charges.
- Forward spam that is phishing for information to spam@uce.gov and to the company, bank, or organization impersonated in the phishing email. You also may report phishing email to reportphishing@antiphishing.org, the Anti-Phishing Working Group — a consortium of ISPs, security vendors, financial institutions and law enforcement agencies — uses these reports to fight phishing.
- If you’ve been scammed, visit the Federal Trade Commission’s Identity Theft website at www.consumer.gov/idtheft.
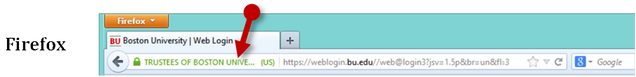
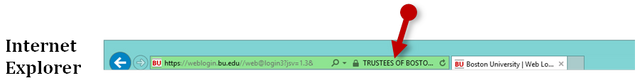
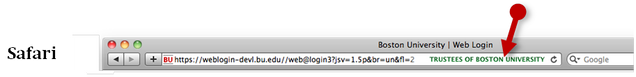
Know The Real So You Can Spot The Fake
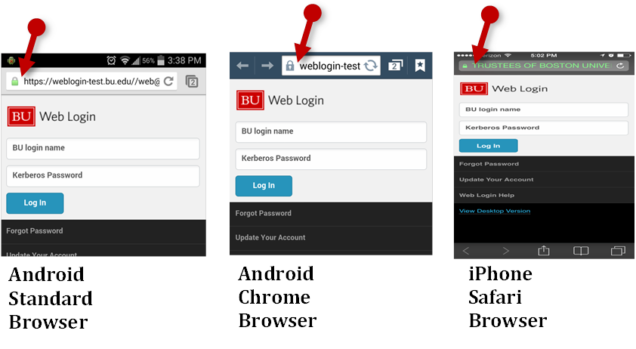
Boston University uses Extended Validation Certificates, be on the lookout for its appearance in various browsers:


Learn how to detect a phishing message & fight phishing
Know the top spam scams, so you can recognize them when you see them.
The email asks for your password
It is a scam. Delete it. You will never be asked for your account password from a legitimate source.
The email is about a financial account you don't have or an order you know nothing about
Typically, phishers send an e-mail or pop-up message that claims to be from a business or organization that you may deal with — for example, an Internet service provider (ISP), bank, online auction service, online payment service, travel service, or even a government agency.
The message may ask you to update, validate, or confirm your account information. Some phishing emails threaten a dire consequence if you don’t respond. The messages direct you to a website that looks just like a legitimate organization’s site. It is almost certain a scam and could look something like this:
“We suspect an unauthorized transaction on your account. To ensure that your account is not compromised, please click the link below and confirm your identity.”
-Or-
“During our regular verification of accounts, we couldn’t verify your information. Please click here to update and verify your information.”
The email comes with an attachment you weren't expecting
These files can contain viruses or other software that can weaken your computer’s security.
They may be videos sent to you from a friend’s account that has been compromised. They may be PDF files from some company claiming to contain an invoice from a recent purchase you did not actually make. They might be “screen savers” or executables masquerading as any number of believable things.
Know what is normal for you, so you can recognize the abnormal.
The email has obvious grammatical or spelling errors
Be suspicious of email messages that claim to be from a business and yet contain errors in grammar, use of words, spelling or punctuation should send you a red flag. Most businesses have several layers of review before a message is approved for release to the public. Obvious errors will typically be caught and removed during this process.
Learn how to detect a SMiShing test and be on the lookout:
Things you can do to avoid being a victim of a SMiShing attempt include:
- Never click links, reply to text messages or call numbers you don’t recognize.
- Do not respond, even if the message requests that you “text STOP” to end messages.
- Delete all suspicious texts.
- Make sure your smart device OS and security apps are updated to the latest version.
- Consider installing anti-malware software on your device for added security.
Spam & Phishing on Social Networks
Spam, phishing and other scams aren’t limited to just email. They’re also prevalent on social networking sites. The same rules apply on social networks: When in doubt, throw it out. This rule applies to links in online ads, status updates, tweets and other posts. Here are ways to report spam and phishing on major social networks:
- Reporting spam and phishing on Facebook
- Reporting spam on Twitter
- Reporting spam and phishing on YouTube
Reporting Phishing at Boston University
If you believe you have received a phishing message, particularly one falsely claiming to be from BU forward it to abuse@bu.edu along with the message headers and then delete it. If in doubt, call the IT Help Center (Charles River Campus (617) 353-4357, Medical Campus (617) 638-5914).
STUDENTS: Download and launch our interactive training “How to Fight Phish”:
FACULTY & STAFF: Take our interactive training “Information Security Awareness: Phishing”
Available to all Faculty and Staff on Boston University’s web-based learning platform Terrier eDevelopment. The training will walk you through what to watch out for with examples and then test you knowledge-can you spot the phish. This training is an excellent tool for teams and departments to use as an awareness and education opportunity in addressing one of the University’s biggest risks!
Take the training now: Information Security Awareness: Phishing (estimated training time: 15 minutes)