National Cybersecurity Awareness Week 2016: October 3-7, 2016
Day 5: Preventing Device Theft
With an increasing amount of sensitive data being stored on personal devices, the value and mobility of smartphones, tablets, and laptops make them appealing and easy targets. These simple tips will help you be prepared in case your laptop is stolen or your smartphone is misplaced.
- Don’t leave your device alone, even for a minute! If you’re not using it, lock your device in a cabinet or drawer, use a security cable, or take it with you. It’s not enough to simply ask the stranger next to you in a library or coffee shop to watch your laptop for a few minutes.
- Differentiate your device. It’s less likely that someone will steal your device and say they thought it belonged to them if your device looks unique. Sometimes these markings make the laptop harder to resell, so they’re less likely to be stolen. Use a permanent marking, engraving, or tamper-resistant commercial asset tracking tag.
- Delete sensitive information. Don’t keep any restricted data on your laptop. We recommend searching your computer for restricted data and deleting it. Restricted data includes your Social Security number, credit card numbers, network IDs, passwords, and other personally identifiable information. You’d be surprised how easy it is to forget that this information is on your computer!
- Back it up. Set a reminder to backup your data on a regular basis! Keep an external copy of important files stored on your laptop in a safe location in case it is lost or stolen. Your photos, papers, research, and other files are irreplaceable, and losing them may be worse than losing your device.
- Encrypt information. Protect your personal data with the built-in disc encryption feature included with your computer’s operating system (e.g., BitLocker or FileVault).
- Record the serial number. Jot down the serial number of your device and store it in a safe place. This information can be useful for verifying your device if it’s found.
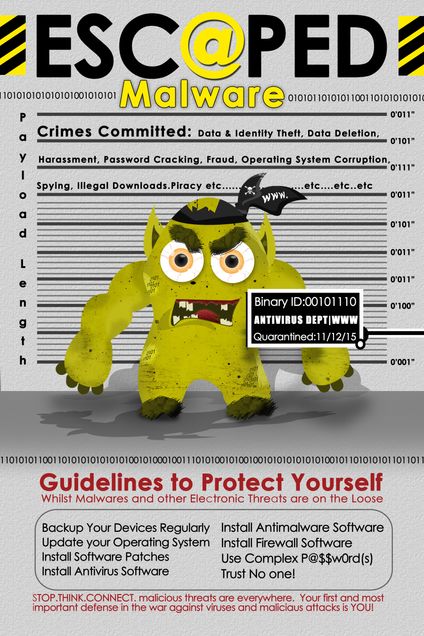
- Install software. Install and use tracking and recovery software included with most devices (e.g., the “Find iDevice” feature in iOS) or invest in commercial products like LoJack or Prey. Some software includes remote-wipe capabilities. This feature allows you to log on to an online account and delete all of the information on your laptop. There are both paid and free versions of this type of software, and each provides different levels of features. Search online to find the best combination of cost and functions to meet your needs.
Day 4: Securing Mobile Devices
Mobile devices have become one of the primary ways we communicate and interact with each other. The power of a computer is now at our fingertips, allowing us to bank, shop, view medical history, attend to work remotely, and communicate virtually anywhere. With all these convenient features come added risks, but here are some tips to protect your devices and your personal information.
- Password-protect your devices. Give yourself more time to protect your data and remote wipe your device if it’s lost or stolen by enabling passwords, PINs, fingerprint scans, or other forms of authentication.
- Secure those devices and backup data! Make sure that you can remotely lock or wipe each mobile device. That also means backing up data on each device in case you need to use the remote wipe function.
- Verify app permissions. Don’t forget to review app specifications and privacy permissions before installing it!
- Update operating systems. Security fixes or patches for mobile devices’ operating systems are often included in these updates.
- Be cautious of public Wi-Fi hot spots. Avoid financial or other sensitive transactions while connected to public Wi-Fi hot spots.
Day 3: Will Your Password Be Unbroken?
Did you know that most passwords are easily broken? Have you found it hard to create a good, strong password that you can remember? Creating a strong, but easily remembered, password can be a challenge, but a few “secrets” can help you. Check out the dos and don’ts below.
Dos
Do you want to create a strong password? (Your answer should be YES.)
- Use at least 8 characters, preferably more
- Use a mix of upper and lower case letters, numbers, and symbols
- Create an easy-to-remember passphrase by choosing a phrase and adding numbers and symbols. Length is more important than complexity. For example:
- “It might seem crazy what I’m about to say” becomes “Itmightseem7CrazywhatI’mabout56to$ay”
- Fairly easy to remember, but far stronger than a typical complex password such as 79RtiO)m^B or something similar
- Consider using a password safe or manager such as LastPass or KeePass
- Change your password or passphrase regularly
- Be sure you’re on the correct website before entering your password or passphrase
Don’ts
- You won’t do these things we’re asking you not to do, will you? (Your answer should be NO.)
- Don’t include your username or account number in your password or passphrase
- Don’t use the same password for multiple services
- Don’t use a single word, in any language
- Don’t use consecutive repeating characters or a number sequence
- Don’t use your pet’s name
- Don’t use your birthdate, address, phone number, or any other type of information someone can easily obtain
- Don’t share your password or passphrase
Day 2: Managing Your Online Reputation
You should understand how to present yourself on social networking sites and how to safeguard your information. What many may consider temporary or fleeting will most likely remain on the Internet forever. As a result, keep these dos and don’ts in mind when sharing online.
Dos
- Ask questions about who can access the information you are posting online, who controls and owns the information, and what is shared with third party.
- Maintain a backup of the content you post on professional networking sites (e.g., LinkedIn).
- Understand the default privacy settings on the social networking sites you use and how to change them to match your comfort level.
- Keep your personal information private. Assess whether it’s necessary to share sensitive information such as your birthday, mailing address, phone number, e-mail, mother’s maiden name, sexual orientation, or Social Security number.
- Be cautious about accepting requests to connect online. Connect only to people you trust who will not misuse the information you post.
- Check the location settings on photos and videos you post to social networking sites.
- Avoid joining online groups where you don’t know all the members or what they stand for.
- Use passphrases to protect your social media accounts. A passphrase is a set of words that create a phrase that is 20 to 30 characters long.
Don’ts
- Don’t share too much information that could be used to complete a profile about you. For example, share your birthday, but not the year you were born. Or share your hometown, but not the address where you live.
- Don’t share any information that is being used for verification purposes such as your mother’s maiden name, the name of your first pet, or the street where first lived. Consider making up alternate answers to those questions that only you would know.
- Don’t post when you are traveling or going out of town on vacation. It’s an open invitation letting criminals know that you are in a different location and that your home is vacant.
- Don’t post photos of inappropriate or illegal activities.
- Don’t click on attachments or links without checking the source.
- Don’t “check in” to every place you visit. That information could be used to identify you in a vulnerable location.
- Don’t use weak passwords, and never share your passwords!
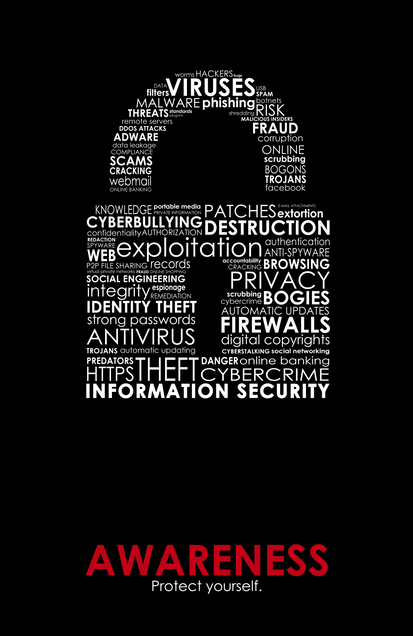
Day 1: Welcome to Information Security Awareness Week!
Throughout the week, we’ll be sending out some brief emails and updating this page with some helpful Information Security pointers. For several years, colleges and universities have promoted cyber security in the month of October (as October is National Cyber Security Awareness Month) as part of a collaborative effort to ensure everyone has the resources they need to stay safe online.
It is important for each of us to be aware of the increasing security risks of mobile devices, from laptops and tablets to smartphones and wearable technology, and 24/7 access to our personal data.
* Protect Your Device: Add a passcode to your cell phone, tablet, or laptop right now!
* Use Strong Passwords or Passphrases: Especially for online banking and other important accounts.
* Check Your Social Media Settings: Review your social media security and privacy settings frequently. Enable two-step verification whenever possible.
* Educate Yourself: Stay informed about the latest technology trends and security issues such as malware and phishing.
* Get Trained: Contact your institution’s IT, information security, or privacy office for additional resources or training opportunities.